Uses, challenges and tradeoffs in working with vector engines.
A search is underway across the industry to find the best way to speed up machine learning applications, and optimizing hardware for vector instructions is gaining traction as a key element in that effort.
Vector instructions are a class of instructions that enable parallel processing of data sets. An entire array of integers or floating point numbers is processed in a single…
The art of ISA design is the fine balance between gaining performance advantages and enhanced usability
The topic of RISC-V custom instructions is growing in importance. This article explains why this subject is becoming so significant, and outlines some of the previous approaches to processor hardware and software optimization to illustrate the techniques that are now possible with RISC-V.…
Simulation is no longer up to the task of system-level verification, but making the switch to hardware-assisted verification can lead to some surprises if you do not fully plan ahead.
Emulation is emerging as the tool of choice for complex and large designs, but companies that swap from simulation to emulation increasingly recognize this is not an easy transition. It requires money, time, and effort, and even then not everyone gets it right.…
Building an open-source verification environment is not an easy or cheap task. It remains unclear who is willing to pay for it
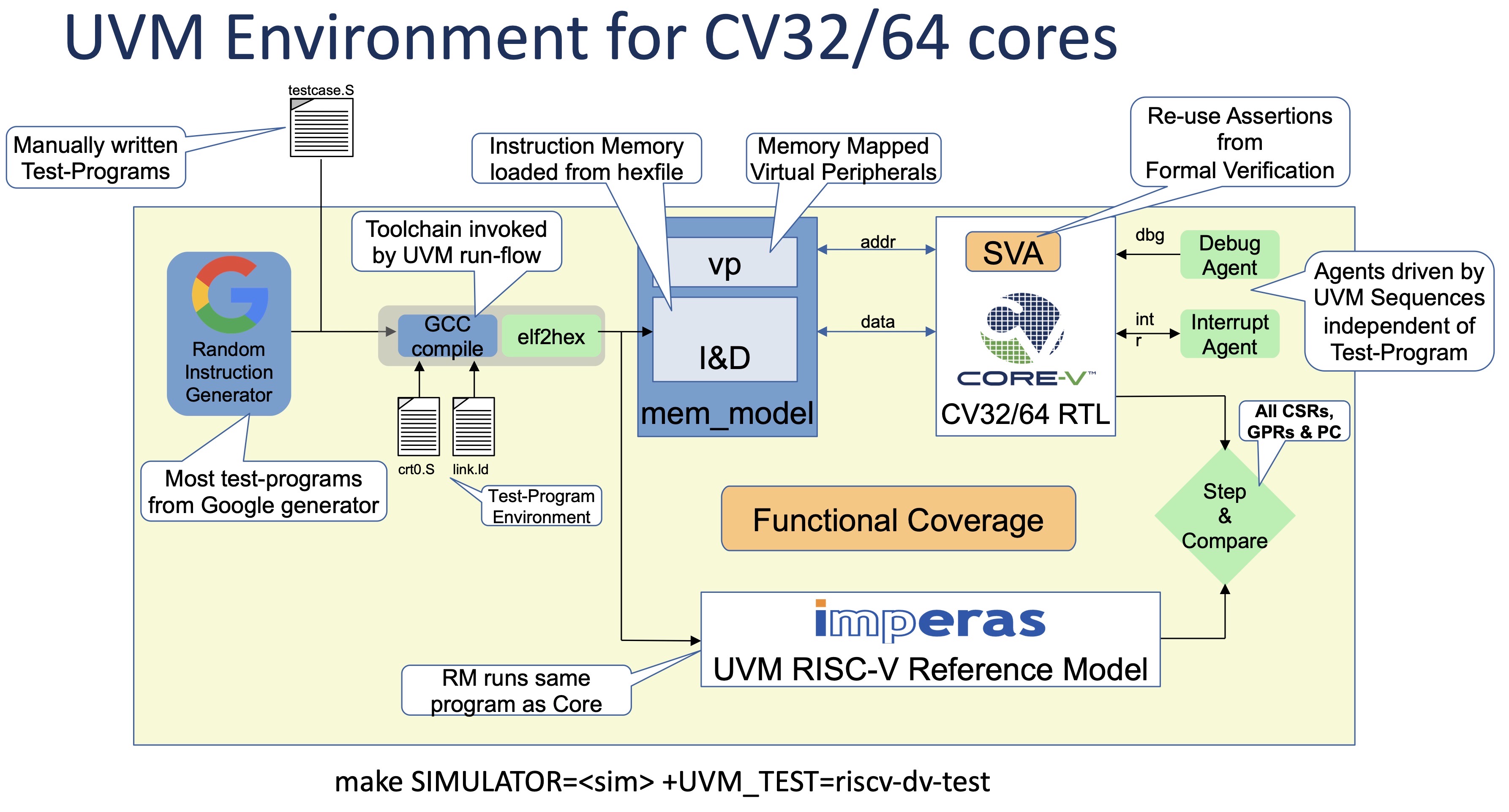
Defining an open-source verification methodology is a lot more difficult than just developing an open-source simulator. This is the reality facing open-source hardware such as RISC-V. Some people may be asking for the corresponding open-source verification, but that is a much tougher problem — and it is not going to be…
The open specification of the RISC-V ISA (Instruction Set Architecture) permits a range of possibilities for processor implementation with a modular approach for standard and custom extensions. In addition, implementations may be shared commercially or as open source, and adopters beyond the original design team can use these directly or as a basis for further modifications…
Sorting out what is meant by open-source verification is not easy, but it leaves the door open to new approaches
Ask different people what open-source verification means and you will get a host of different answers. They range from the verification of open-source hardware, to providing an open-source verification infrastructure, to providing open-source stream generators or reference models, to open-source simulators and formal verification engines.
…
It has been an unusual DAC this year, as the show went virtual due to the Covid-19 pandemic. There was no exhibition floor as such, but there was a comprehensive programme of keynote speeches, presentations, tutorials and panel discussions
There was a lot of activity around RISC-V, including a presentation by Imperas Software (www.imperas.com) entitled ‘What’s Next for RISC-V? Vectors, Verification, and…
The July 2020 edition of Mentor Graphics', a Siemens Business, Verification Horizons article and Verification Academy presentation on RISC-V Processor DV are now available online
As SoC developers adopt RISC-V and the design freedoms that an Open ISA (Instruction Set Architecture) offers, DV teams will need to address the new verification challenges of RISC-V based…
RISC-V drives new attention to this market, but the cost/benefit equation is different for open-source hardware than software
Open-source hardware continues to gain ground, spearheaded by RISC-V — despite the fact that this processor technology is neither free nor simple to use.
Nevertheless, the open-source hardware movement has established a solid foothold after multiple prior forays that yielded only limited success, even for processors. With demand…